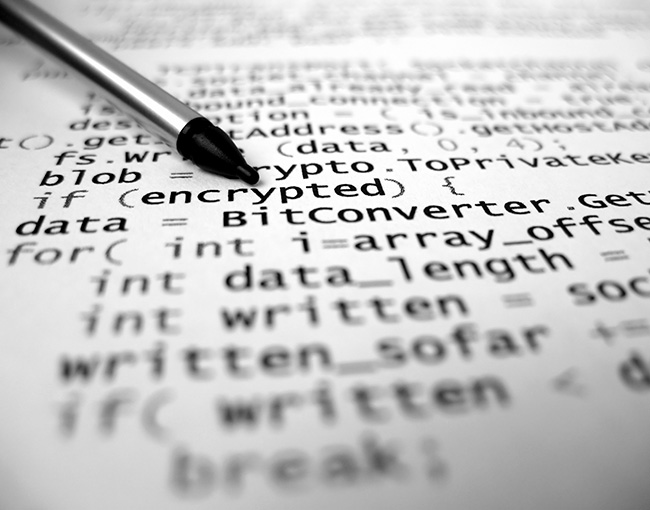
In the new reality of transparent data collection, use, and security, companies may be forced to strike a careful balance between protecting their confidential and privileged information and complying with various laws requiring them to be transparent and to keep consumers informed. READ MORE